Why Manual Documentation is Breaking Regulated Engineering Teams

Imagine an auditor asks to see the exact documentation state for a specific software release from two years ago. Not the current docs. The docs as they were on the day you shipped that version.
If your team is like most, that question lands like a small emergency.
Someone starts searching shared drives. Someone else checks Confluence. A third person opens a spreadsheet that may or may not have been updated after the last release. The documentation exists, probably, somewhere. But whether it accurately reflects the software at that moment, with the right version numbers, the right approvals, the right rationale for every change? That's harder to prove.
This is the gap that breaks documentation systems in regulated industries. Regulators don't just want good documentation. They want a provable chain of evidence, maintained continuously, with the metadata to prove it was maintained. Most modern documentation tools weren't built for that. Most engineering workflows weren't designed around it. And the teams caught in the middle end up spending enormous effort on a process that satisfies no one.
What Auditors Actually Want
The word "traceability" gets used a lot in regulated software contexts, but it's worth being specific about what it means in practice.
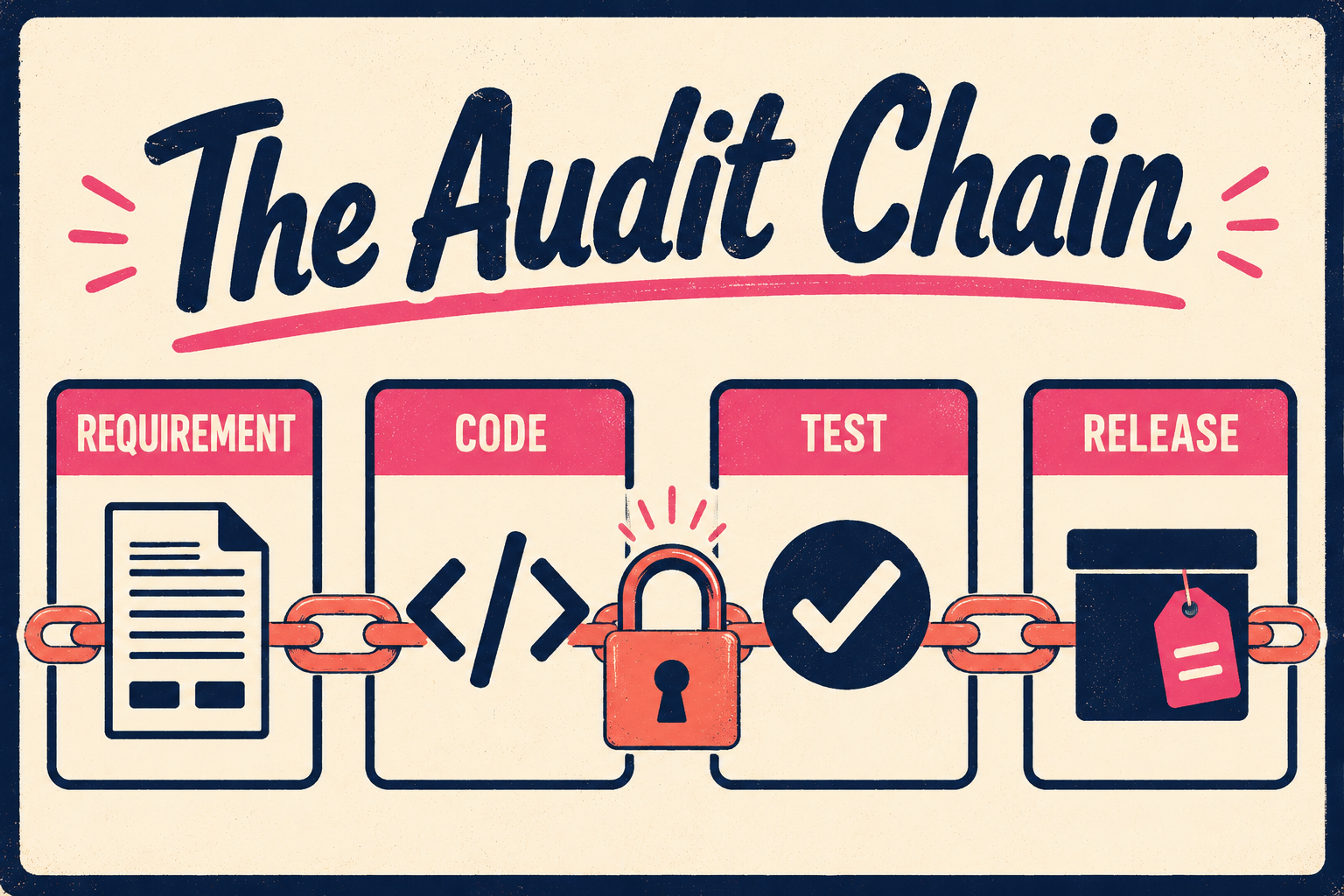
An auditor reviewing a medical device submission isn't looking for a well-written user manual. They're looking for a chain: a specific requirement, linked to the code that implements it, linked to the test that verifies it, linked to the release artifact that documents it. Every link in that chain needs to be provable, and the chain needs to be complete.
The FDA's guidance on premarket submissions for device software functions is explicit about this. Documentation of requirements must include adequate detail to support traceability among requirements, specifications, identified hazards and mitigations, and verification and validation activities. An FDA 510(k) submission requires that every claim about device behavior in the user manual be traceable to a specific test protocol and result.
Aviation is similarly demanding. The DO-178C avionics standard requires comprehensive traceability from system-level requirements to all testing and verification evidence, including who did what, when, and to which artifact. The challenge, as researchers working with aerospace professionals have noted, is not the content itself but the evidence chain. If there is source code that cannot be traced back to a requirement, it's a compliance failure, not a documentation gap.
The automotive standard ISO 26262 demands bidirectional traceability from hazard analysis through requirements, design, implementation, and verification. Defense contractors working under CMMC 2.0 Level 2 must create and retain system audit logs and records sufficient to enable monitoring, analysis, investigation, and reporting of unauthorized activity, and their System Security Plan must accurately reflect the current state of the system at all times.
Across all of these frameworks, the pattern is the same. Auditors want metadata: who made the change, when, who approved it, and why. They want it retained. They want it linked to the artifact it describes.
Where the Process Breaks
Most teams maintain traceability in external artifacts: spreadsheets, traceability matrices, or fields in ALM tools like Jira, Codebeamer, or IBM DOORS. These tools exist outside the codebase. They describe intended relationships but don't participate in the development workflow in a way that enforces consistency.
A developer can delete a function that implements a requirement without any signal from the traceability system. A requirement can be renamed in the ALM tool without any corresponding update to the code or tests. Research on this problem found that 80% of practitioners identified cost as the primary barrier to traceability adoption, with manual maintenance burden cited as the dominant contributor. The result is traceability debt that accumulates silently and surfaces during audits.
The same fragility applies to change control. SOC 2 Trust Services Criteria CC8.1 requires formal approval before any change reaches production, with documentation of who requested it, who approved it, and what the impact analysis showed. PCI DSS Requirement 6.5 requires that significant changes to systems in scope, including new software, hardware, or changes to the cardholder data environment, trigger updated documentation, network diagrams, and vulnerability scans before deployment.

When these records are maintained in disconnected systems, they fall out of sync with the codebase. The documentation says one thing; the software does another. Closing that gap before an audit is expensive, stressful, and often incomplete.
Validation adds another layer. The FDA's General Principles of Software Validation define validation as establishing documented evidence that provides a high degree of assurance a specific process will consistently produce a product meeting its predetermined specifications. That means review processes need to be documented too: who reviewed what, what criteria they applied, and how the approval was recorded.
HIPAA's Security Rule requires hardware, software, and procedural mechanisms that record and examine activity in information systems. Covered entities must retain compliance documentation, policies, and procedures for at least six years from the date of creation or the date last in effect. FDA 21 CFR Part 11 requires secure, computer-generated, time-stamped audit trails that independently record the date and time of operator entries and actions that create, modify, or delete electronic records.
The retention requirements alone are significant. But the harder problem is that the records need to be accurate and retrievable, not just stored. A six-year-old Word document in a shared drive is not the same as a versioned, immutable record linked to the release it describes.
What the Standards Actually Say
It's worth being concrete about the specific documentation requirements, because the gap between what teams produce and what auditors expect is often larger than teams realize.
For a medical device 510(k) submission, the FDA requires traceability among requirements, specifications, identified hazards and mitigations, and verification and validation activities. The user manual's claims about device behavior must be traceable to specific test protocols and results. If the manual says a device will alert when a threshold is exceeded, there must be a documented test proving that alert fires under those exact conditions, and the requirement, code, test, and manual must all be linked.
For aviation software certified under DO-178C, the standard demands that high-level requirements are developed into low-level requirements, which are developed into source code, with full bidirectional traceability between requirements, test cases, test procedures, and test results. Researchers working with aerospace industry professionals have confirmed that this traceability work is currently performed mostly as a manual activity at the end of the project, which blocks agile delivery and creates the conditions for documentation that doesn't accurately reflect the software it describes.
For defense contractors, CMMC Level 2 requires a System Security Plan that accurately describes the system and its controls. The plan must be kept current. An SSP that describes a system as it existed eighteen months ago is not a compliant SSP.
The Agile V framework, developed by researchers studying compliance-oriented engineering, found that the traditional approach requires three to five days of dedicated compliance effort per project just to produce the core documents: requirements specification, traceability matrix, test execution log, decision rationale, risk register, and validation summary. That's before any of the documentation is reviewed, approved, or archived.
Anyway. The documentation burden in regulated industries isn't a paperwork problem. It's a structural problem. The evidence chain that auditors require is built on artifacts that are created separately from the engineering work, maintained manually, and drift from the codebase the moment development accelerates.
Engineering teams in regulated industries need release notes, API references, and changelogs that meet compliance standards: human-verified, traceable, and audit-ready. Building that by hand for every release is unsustainable at the pace modern teams ship. Doc Holiday generates those artifacts directly from engineering workflows, with the structure to validate, govern, and archive output in a way that satisfies auditors. It gives compliance and QA leaders the system their best technical writer can run and verify, so the evidence chain is a byproduct of development rather than a separate effort that happens after the fact.