API Documentation Requirements for Healthcare Software: What Actually Gets Reviewed in a HIPAA Audit

Healthcare APIs occupy a peculiar position in the compliance landscape. They are technical artifacts — endpoints, schemas, authentication flows — but the moment they touch Protected Health Information (PHI), they become compliance artifacts too. The documentation that describes them must serve two audiences with fundamentally different needs: the developer integrating with the API and the compliance officer who will be asked to sign off on it during an audit.
The gap between those two audiences is where most healthcare engineering teams get into trouble.
When an auditor from the Office for Civil Rights (OCR) asks to see your API documentation during a HIPAA assessment, a Swagger file is not the answer. Swagger files describe what an API does. Auditors need evidence of how it protects PHI — authentication flows mapped to access control requirements, encryption standards specified in terms that satisfy the Security Rule's technical safeguards, and breach notification procedures that demonstrate your team knows what to do when something goes wrong. That evidence has to be written in plain language that a non-technical compliance officer can evaluate, not just a developer can implement.
This is the operational reality facing engineering leaders in healthcare: the documentation burden is substantial, the compliance stakes are high, and the teams responsible for producing that documentation are often the same teams building the software under tight timelines.
Authentication and Authorization Documentation
The HIPAA Security Rule requires covered entities and business associates to implement technical policies and procedures that allow only authorized persons to access ePHI (45 CFR § 164.312(a)(1)). For an API, that requirement translates directly into documentation obligations that go well beyond listing which endpoints require a token.
Healthcare API documentation must describe the complete authentication model: which OAuth 2.0 grant types are supported, how access tokens are scoped to limit PHI exposure, how token expiration is enforced, and what happens when a refresh token is used. The HL7 FHIR security specifications recommend OAuth 2.0 and the SMART App Launch framework as the standard approach for healthcare APIs (HL7, 2024), and documentation should explicitly reference these standards to give auditors a compliance anchor.
But the more important distinction — the one that separates documentation that satisfies a compliance officer from documentation that only satisfies a developer — is the difference between documenting the technical implementation and documenting the security model. "Endpoint X requires a Bearer token with the patient.read scope" is a technical fact. "Access to Endpoint X is restricted to authenticated users whose scope has been verified against the patient's record, ensuring the minimum necessary PHI is exposed" is a compliance statement. Healthcare API documentation needs both layers, and they need to be clearly connected.
There is also a specific risk that documentation must address: Broken Object Level Authorization (BOLA) vulnerabilities, where an authenticated user can access PHI belonging to another patient by manipulating resource identifiers. Security researchers have documented this as one of the most common failure modes in FHIR API implementations (Approov, 2021). Documentation should describe how the API prevents this — not just that it does.
Data Handling and Encryption
The HIPAA Security Rule's transmission security standard (45 CFR § 164.312(e)(1)) requires that ePHI be protected against unauthorized access during electronic transmission. For APIs, this means documentation must specify the exact protocols and cipher standards in use, not just assert that the API is "encrypted."
Minimum requirements that must be documented include TLS 1.2 or higher for all API endpoints (TLS 1.3 preferred), AES-256 encryption for data at rest, and key management procedures that include rotation schedules and access controls (Accountable HQ, 2025). For service-to-service communication, mutual TLS or signed, short-lived JWTs should be documented as the authentication mechanism.
Equally important is the documentation of what the API does not expose. Error messages are a common source of PHI leakage — a poorly designed error response that includes a patient identifier or a record fragment can constitute an impermissible disclosure under the Privacy Rule. API documentation must specify the error handling design: what information is included in error responses, how errors are categorized, and how the system ensures that diagnostic information useful to developers does not expose PHI to unauthorized parties.
The language used throughout this section must be compatible with Business Associate Agreements (BAAs). When a covered entity signs a BAA with a vendor whose API processes PHI, the BAA defines permitted uses and disclosures. API documentation that describes data handling in vague terms creates ambiguity about whether a given use falls within the BAA's scope — and that ambiguity becomes a finding in an audit.
Audit Logging Documentation
The HIPAA Security Rule's audit controls standard (45 CFR § 164.312(b)) requires implementing mechanisms to record and examine activity in systems that contain or use ePHI. For APIs, this requirement has two components: the technical logging implementation and the documentation of that implementation.
API documentation must specify what events are logged, what data elements each log entry contains, how logs are stored and protected, and how long they are retained. HIPAA requires compliance documentation to be retained for a minimum of six years (HHS, 2024), and audit logs fall within that requirement. Documentation should also address the access controls on the logs themselves — who can view them, how access is monitored, and how the logs are protected against tampering.
The table below summarizes the key data elements that HIPAA-compliant API audit logs must capture, as derived from the Security Rule's audit controls standard and NIST SP 800-66 Rev. 2 guidance (NIST, 2024):
One nuance that documentation often misses: logs should avoid containing raw PHI wherever possible. If a patient record identifier is sufficient to reconstruct what was accessed, there is no need to log the actual PHI content. Documentation should specify this design choice explicitly, because it affects both the security of the logs and the organization's exposure if the logs themselves are compromised.
Versioning, Deprecation, and the Change Audit Trail
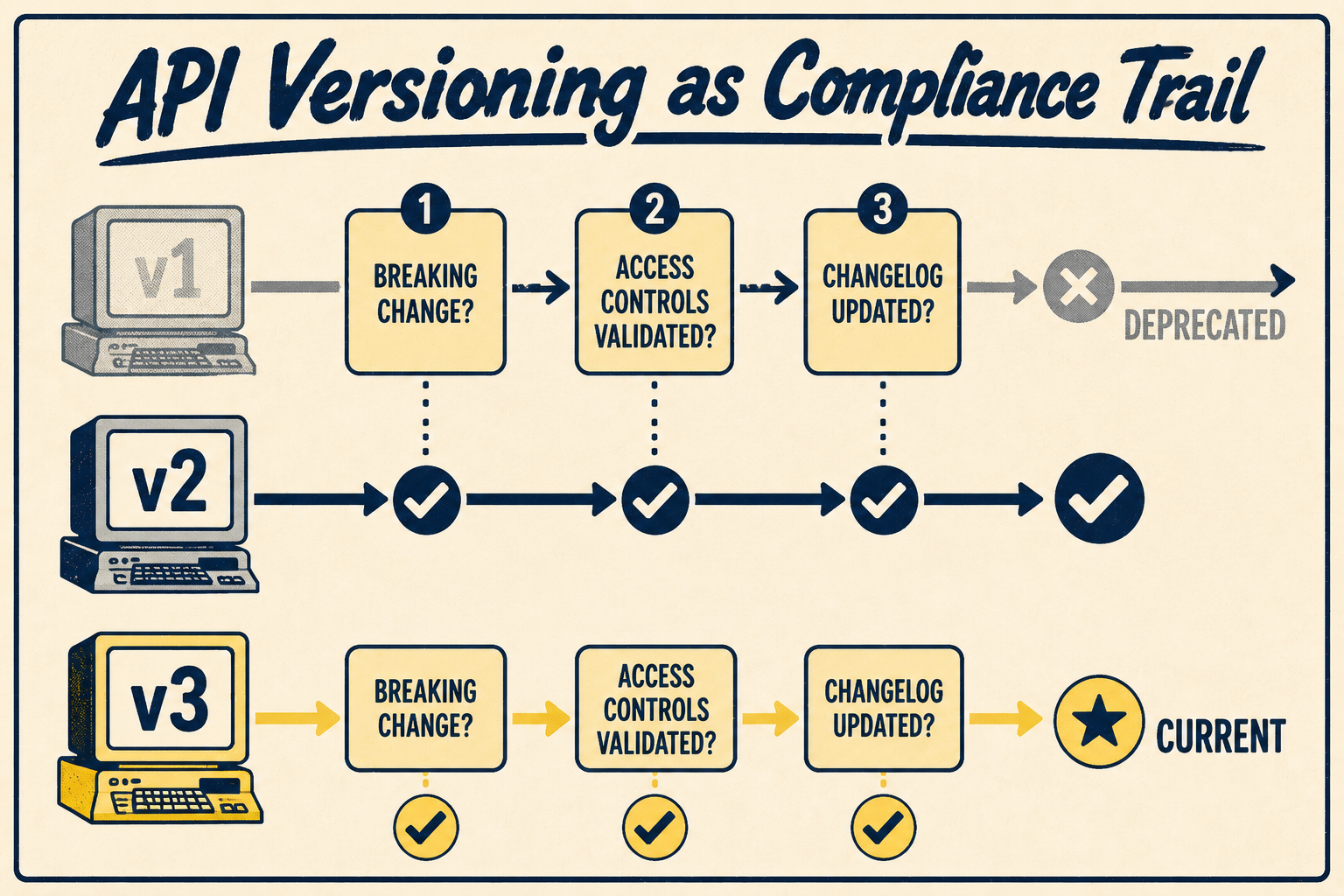
In healthcare software, API versioning is not just a developer experience concern — it is a patient safety and compliance issue. A breaking change to an API that disrupts a clinical workflow, or a deprecated endpoint that continues to accept requests without proper access controls, can create both care delivery failures and compliance gaps.
API documentation must define the versioning strategy clearly: how versions are numbered, what constitutes a breaking change, how long deprecated versions remain active, and how consumers are notified of upcoming changes. The ONC's 21st Century Cures Act Final Rule established requirements for health IT developers to maintain standardized APIs without information blocking (ONC, 2024), which adds a regulatory dimension to deprecation decisions that purely technical API versioning policies do not address.
The change log is also a compliance artifact. When an auditor asks whether PHI access controls have been consistently enforced across API versions, a well-maintained change log provides the evidence. When a security incident occurs and investigators need to determine whether a vulnerability existed at the time of a specific access event, the change log establishes the timeline. Documentation that treats the change log as a developer convenience rather than a compliance record creates gaps that are difficult to close retroactively.
The Documentation Burden Engineering Teams Actually Face
A 2024 Akamai survey found that 84.7% of healthcare organizations experienced API security incidents in the past 12 months, and only 24% of those with full API inventories knew which APIs returned sensitive data (Akamai, 2024). That visibility gap is partly a security problem and partly a documentation problem — organizations cannot protect what they have not documented.
The challenge for engineering leaders is that producing compliant API documentation requires expertise that sits at the intersection of technical writing, healthcare regulation, and security engineering. A developer who writes excellent OpenAPI specifications may not know how to describe an authentication flow in terms that satisfy a compliance officer. A compliance officer who understands HIPAA requirements may not be able to evaluate whether a given technical implementation actually meets them. A technical writer who bridges those two worlds is a specialized role, and specialized roles are expensive.
The practical answer is not to hire a larger documentation team. It is to use systems that generate the right documentation structure from engineering workflows — authentication flows documented with security implications built in, data handling described in BAA-compatible language, error handling designed to protect PHI from the start — and then apply expert validation to what the system produces rather than writing everything from scratch.
A senior technical writer who understands HIPAA can validate and refine system-generated documentation far more efficiently than producing it manually. But that efficiency depends entirely on the system generating the right structure. If the output requires fundamental restructuring before it can be evaluated for compliance, the efficiency gain disappears.
What Doc Holiday Generates for Healthcare API Documentation
Doc Holiday is built for exactly this constraint. It generates endpoint references with built-in compliance context, so the security implications of each endpoint are documented alongside the technical specification rather than in a separate document that may or may not stay synchronized. It produces authentication flow documentation structured around HIPAA requirements, giving compliance officers a starting point for review — not a substitute for it. The output requires validation by someone who understands healthcare regulations before it can be treated as audit-ready evidence; Doc Holiday assists with compliance context but does not replace human judgment or the validation workflows your team already has in place. What it provides is the structure that makes that validation work scalable — across a growing API surface, across multiple versions, and across the multiple audiences that healthcare API documentation must serve. Change logs are maintained as a first-class output rather than an afterthought, creating the audit trail that healthcare systems need without requiring a separate manual process.
The documentation debt that accumulates when healthcare engineering teams try to serve developers, compliance officers, security assessors, and business associates with a single Swagger file is real, and its consequences show up in audits. The path forward is documentation infrastructure that generates the right structure from the start, so the compliance layer can be validated efficiently rather than rebuilt repeatedly.