How Should Teams Approach Writing Internal Vs External Release Notes Differently?

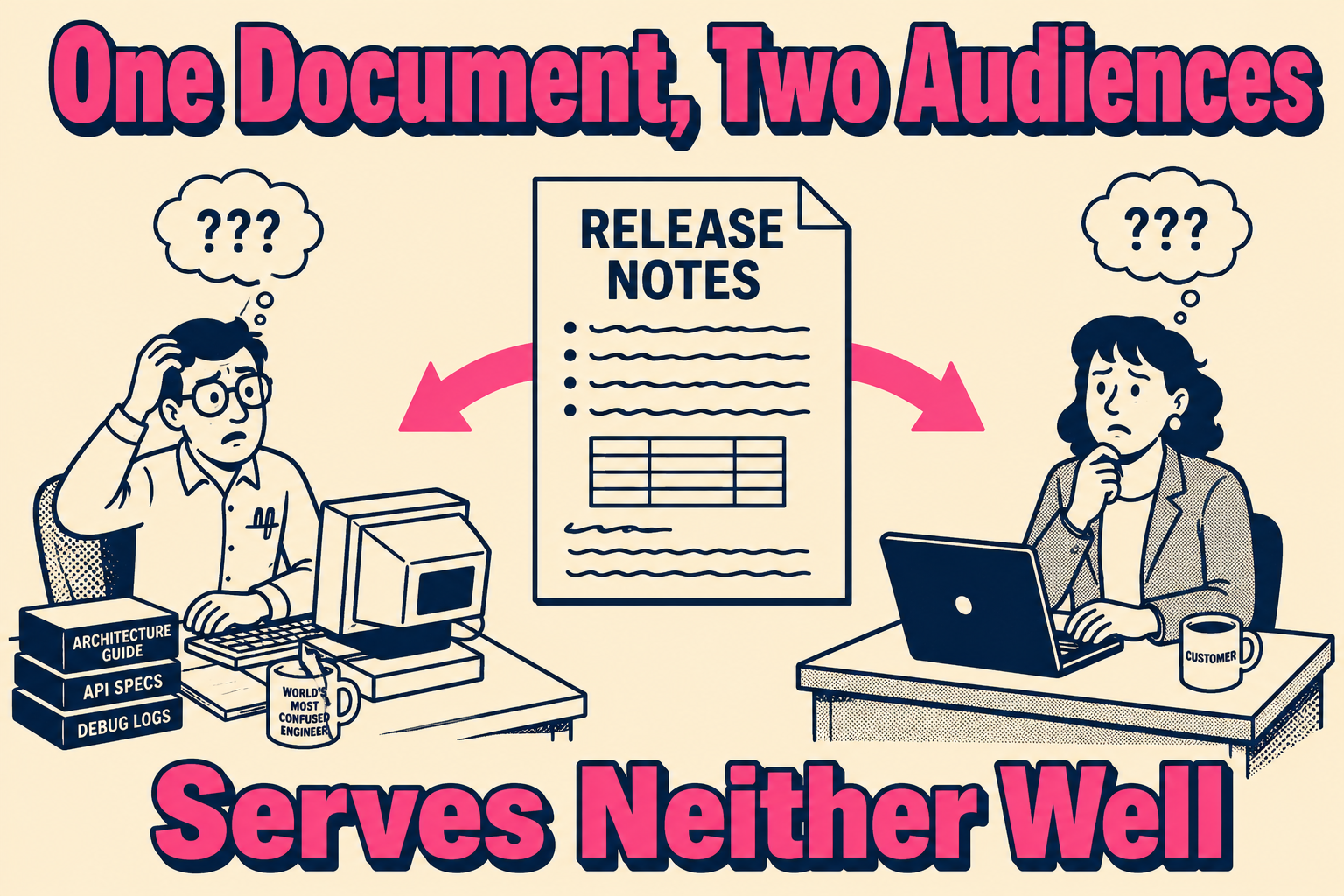
Internal and external release notes are not the same document with different levels of detail. They are different documents with different purposes, different owners, and different failure modes. Treating them as one document with redactions is the most common mistake teams make when they are asked to standardize release note production, and it produces notes that serve neither audience well.
Here is the operational distinction that matters: internal release notes exist so teams do not break each other's work. External release notes exist so customers understand what changed and what they need to do. Those are genuinely different jobs.
Why Conflating Them Creates Problems Downstream
When a team writes one set of release notes and tries to adapt it for two audiences, the result is usually a document that is too vague for engineers and too technical for customers. The engineering team wrote for themselves, and the customer got the raw output.
Research on this problem is consistent. A 2020 study of 32,425 release notes across 1,000 GitHub projects found significant discrepancies between what release note producers think they are communicating and what users actually receive. The documented information is often vague, poorly organized, and offers limited practical assistance. A 2016 study from TU Munich found that different stakeholders (project managers, developers, end users, beta testers) have fundamentally different information needs from the same release, and proposed generating audience-specific views from a single source of truth rather than a single document for everyone.
The timing problem compounds this. Support teams typically receive release notes at the same time as users, or shortly before. That is not enough time to update knowledge base articles, brief agents, or identify which customer segments will be affected. When the notes are written for engineers, support teams cannot extract what they need quickly enough to be useful.
The stakes are not just operational confusion. Internal notes that sound like marketing copy confuse engineers trying to understand what actually changed. External notes that expose implementation details create security and support debt that takes months to unwind.
What Belongs in Internal Release Notes
Internal release notes are a coordination tool. Their job is to reduce the cost of adjacent teams having to ask questions.
That means they should include: technical debt paid down, API changes that affect other services, and config changes ops needs to know about. Breaking changes, deprecations, and rollback procedures. Performance deltas, dependency updates, and schema migrations. Known issues the team is monitoring, including things support will hear about before they are fixed.
The frame to use when writing internal notes is not "what did we ship?" It is "what does another team need to know to keep working without interruption?" If a change requires another team to take action, it belongs in the internal notes, described in enough detail that they can act without a follow-up conversation.
A 2024 analysis of release note challenges on GitHub found that nearly 47% of all reported issues were related to production, specifically the difficulty of automating and standardizing the creation of notes. Content problems, particularly missing information for breaking changes, accounted for another 25%. The missing breaking change is almost always an internal note failure, not an external one.
What Belongs in External Release Notes
External release notes are a customer communication. Their job is to set expectations, reduce ticket volume, and build trust.
They should include value-focused feature announcements framed around what the user can do now that they could not do before. Workflow changes, especially if something moved or behaves differently. Resolved customer-reported bugs, with enough context that the customer who filed the ticket recognizes the fix. Security updates, framed around user action and safety.
What they should not include: implementation details, internal system names, schema changes that have no user-visible effect, or known issues that haven't cleared. The test for whether something belongs in external notes is whether a customer reading it would understand what changed about their experience.
Stripe's approach to API versioning is a useful reference here. Their engineering blog on API versioning describes a system where backwards-incompatible changes are explicitly versioned and communicated to developers with enough lead time to migrate, while the underlying implementation details stay internal. The external communication is about the contract, not the code.
The Security Boundary is the Hardest Part to Get Right
The distinction between internal and external notes is not just about clarity. It is about security.
When vulnerability information propagates from internal systems to public release notes, the risk of information disclosure increases. A 2025 study on vulnerability disclosures in open-source software found that missing or delayed CVE assignments result in projects not being notified of necessary security updates promptly, but the inverse problem is also real: publishing exploit details before users have patched creates a window of exposure.
The OWASP Vulnerability Disclosure Cheat Sheet is explicit about this: organizations should publish clear security advisories and changelogs, but the disclosure should include a high-level summary of the vulnerability and its impact, not technical details or proof-of-concept code until users have had time to patch.
If your external release notes are just redacted versions of your internal notes, you are relying on engineers to remember what is safe to publish. That is a process design problem. Redaction requires someone to know what to remove. Rewriting for the audience requires someone to know what to include. Those are different cognitive tasks, and the second one is safer.
Who Owns What, and When
The governance model matters as much as the content model.
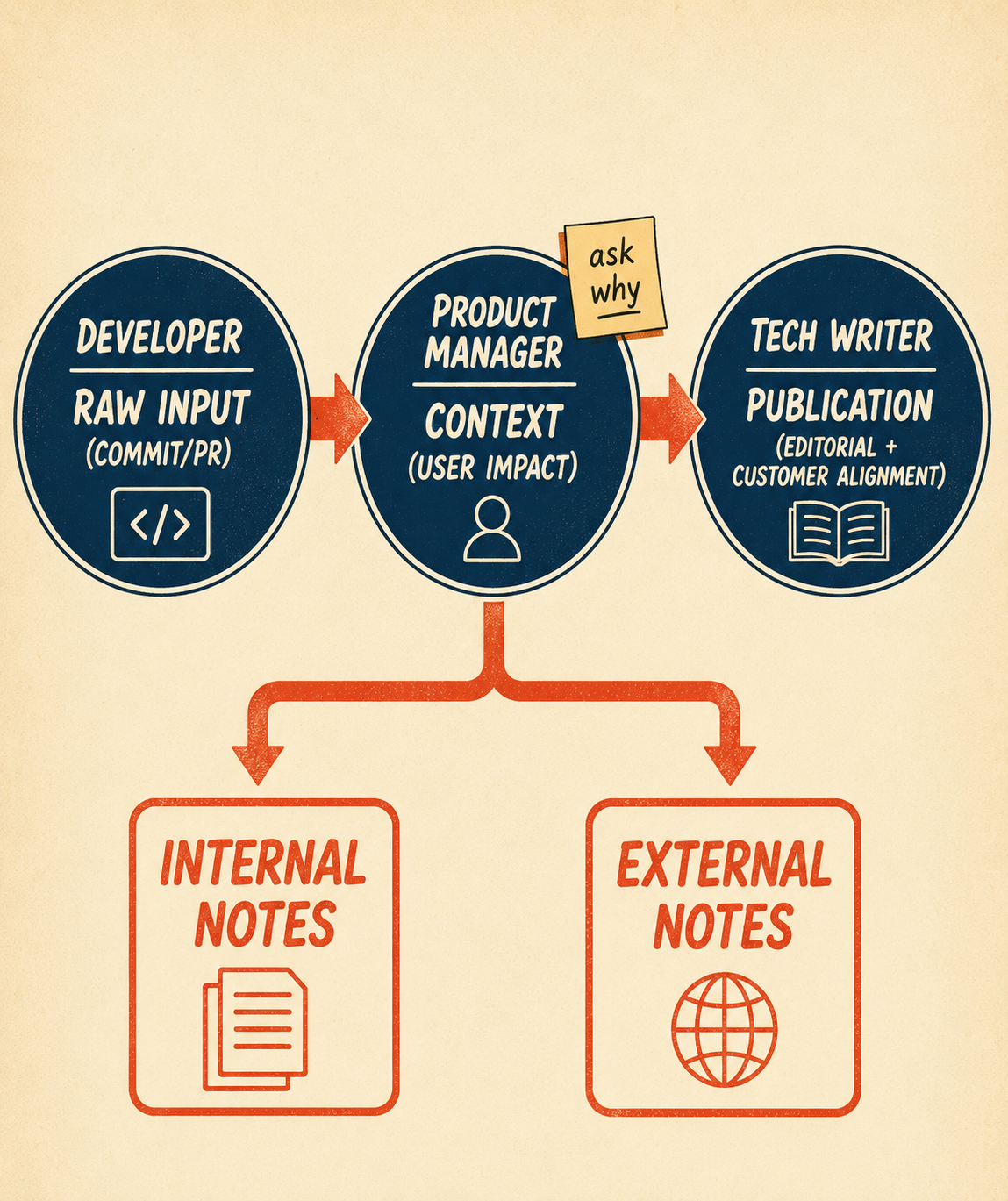
A functioning approach distributes the workload while centralizing the approval. The developer owns the raw input: the commit message or PR description. The product manager owns the context: why this change matters to the user. The documentation owner or technical writer owns the final publication decision, ensuring the note meets editorial standards and aligns with customer-facing communications.
Mozilla's Firefox release management team runs a version of this model at scale. Release management monitors patches that land in the codebase during the nightly development cycle and asks engineering to nominate changes for release note inclusion via a tracking flag in Bugzilla. Engineering nominates; release management curates and publishes. The people closest to the code flag what matters, but they do not write the final customer-facing language.
For multi-product releases where changes span teams, the governance model needs one additional element: a designated cross-team coordinator who owns the consolidated publication. Without this, each team publishes on its own schedule, and customers receive a fragmented picture of what changed.
Where AI Documentation Breaks Down Without Structure
This is where automated release note generation creates a new version of the old problem.
Models pull from commit history and cannot distinguish what is safe to publish externally. A 2025 study presenting the SmartNote system at FSE 2025 found that existing automated tools fail to consider the diverse needs of various audiences and project domains, producing notes that leave specific user groups without critical details while overwhelming others with irrelevant technical information. The system they built generates contextually personalized release notes from code, commit, and pull request details, but the personalization requires knowing which audience each note is for.
The operational model that works is: AI drafts from commits and pull requests, humans review in a structured interface, and the internal/external boundary is enforced by the workflow, not by individual judgment calls at publication time. Pull request data becomes internal notes automatically. A technical writer marks which items need external translation and rewrites them in the same interface.
Doc Holiday is built around this workflow. It generates both internal and external release notes from the same engineering artifacts, then applies boundary rules so nothing crosses over incorrectly. The engineering artifact is the input; the audience-appropriate note is the output. That structure is what makes the security and duplication problems described above solvable without rebuilding the process from scratch every release cycle.